January 12, 2014
Safe Scripting with Sandboxing
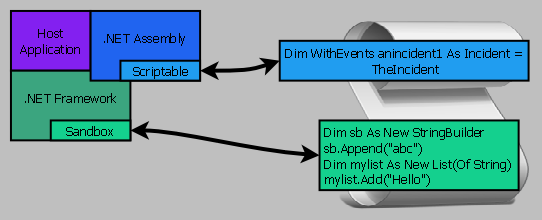
Restrict script access to the safe subset of the .NET framework.
Safe End-User Scripting:
- Block unsafe script instructions by setting Sandboxed property
- Allow script access to safe .NET functionality
- Permit language extensions marked as Scriptable
- Protect server applications from unsafe scripts
-
Safe scripting in a .NET application provides powerful .NET script access without compromising functionality.
Windows desktop and server applications can be safely scripted by end-users.
- Allow end-user's to safely script server applications
- Simplify scripts to a restricted subset of the .NET framework.
Server-side scripts are protected from unsafe use of the .NET framework.